AWS Security Blog
Tag: IAM
How to monitor and query IAM resources at scale – Part 1
March 7, 2023: We’ve fixed a typo in the blog post. In this two-part blog post, we’ll provide recommendations for using AWS Identity and Access Management (IAM) APIs, and we’ll share useful details on how IAM works so that you can use it more effectively. For example, you might be creating new IAM resources such as roles […]
The anatomy of ransomware event targeting data residing in Amazon S3
Ransomware events have significantly increased over the past several years and captured worldwide attention. Traditional ransomware events affect mostly infrastructure resources like servers, databases, and connected file systems. However, there are also non-traditional events that you may not be as familiar with, such as ransomware events that target data stored in Amazon Simple Storage Service […]
How to revoke federated users’ active AWS sessions
February 6, 2023: Updates added to explain an additional detail regarding the sourceIdentity field. In addition to using the sourceIdentity field to reference the user through various roles they have assumed, you may also construct your IAM trust policies to enforce acceptable sourceIdentity values or ensure any value for sourceIdentity is set. When you use […]
How to secure your SaaS tenant data in DynamoDB with ABAC and client-side encryption
If you’re a SaaS vendor, you may need to store and process personal and sensitive data for large numbers of customers across different geographies. When processing sensitive data at scale, you have an increased responsibility to secure this data end-to-end. Client-side encryption of data, such as your customers’ contact information, provides an additional mechanism that […]
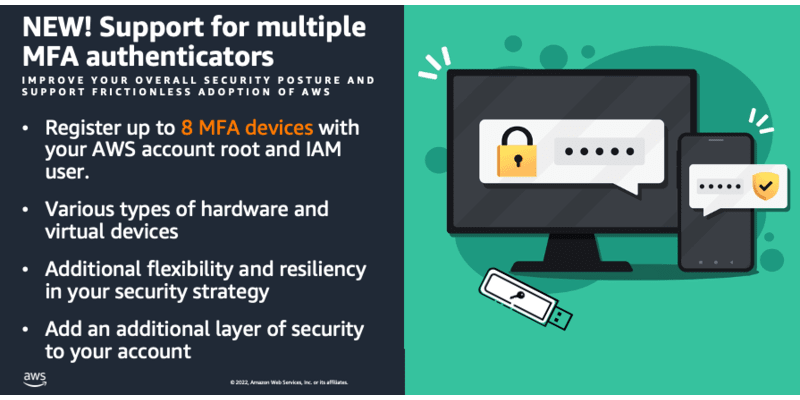
You can now assign multiple MFA devices in IAM
November 17, 2025: The MFA Security Key program, which provided eligible customers with free MFA devices, has been discontinued effective November 6th, 2025. While existing devices will continue to function normally, no new orders for MFA security keys will be accepted after the program closure date. At Amazon Web Services (AWS), security is our top […]
Announcing an update to IAM role trust policy behavior
April 16, 2024: Updated with information on AWS CloudTrail logging for roles that are still using the implicit trust behavior, and additional sample queries to find these roles. June 15, 2023: Enforcement has changed from a fixed date to an automated process starting June 30, 2023 that removed roles based on observed role assumption behavior. […]
How to let builders create IAM resources while improving security and agility for your organization
September 7, 2022: The post was updated to rephrase the brief of creating builder role with the builder policy attached as the permissions policy. Many organizations restrict permissions to create and manage AWS Identity and Access Management (IAM) resources to a group of privileged users or a central team. This post explains how you can […]
How to centralize findings and automate deletion for unused IAM roles
Maintaining AWS Identity and Access Management (IAM) resources is similar to keeping your garden healthy over time. Having visibility into your IAM resources, especially the resources that are no longer used, is important to keep your AWS environment secure. Proactively detecting and responding to unused IAM roles helps you prevent unauthorized entities from gaining access […]
Scale your workforce access management with AWS IAM Identity Center (previously known as AWS SSO)
AWS Single Sign-On (AWS SSO) is now AWS IAM Identity Center. Amazon Web Services (AWS) is changing the name to highlight the service’s foundation in AWS Identity and Access Management (IAM), to better reflect its full set of capabilities, and to reinforce its recommended role as the central place to manage access across AWS accounts […]
Extend AWS IAM roles to workloads outside of AWS with IAM Roles Anywhere
AWS Identity and Access Management (IAM) has now made it easier for you to use IAM roles for your workloads that are running outside of AWS, with the release of IAM Roles Anywhere. This feature extends the capabilities of IAM roles to workloads outside of AWS. You can use IAM Roles Anywhere to provide a […]