AWS Security Blog
Category: Intermediate (200)
ACM will no longer cross sign certificates with Starfield Class 2 starting August 2024
February 20, 2026: We updated the first question in the FAQ to list to add Amazon ClodFront as a representative AWS service with an example. This is not the full list of services that consume certificates from ACM and should only be used as a reference. November 13, 2025: We updated the first question in […]
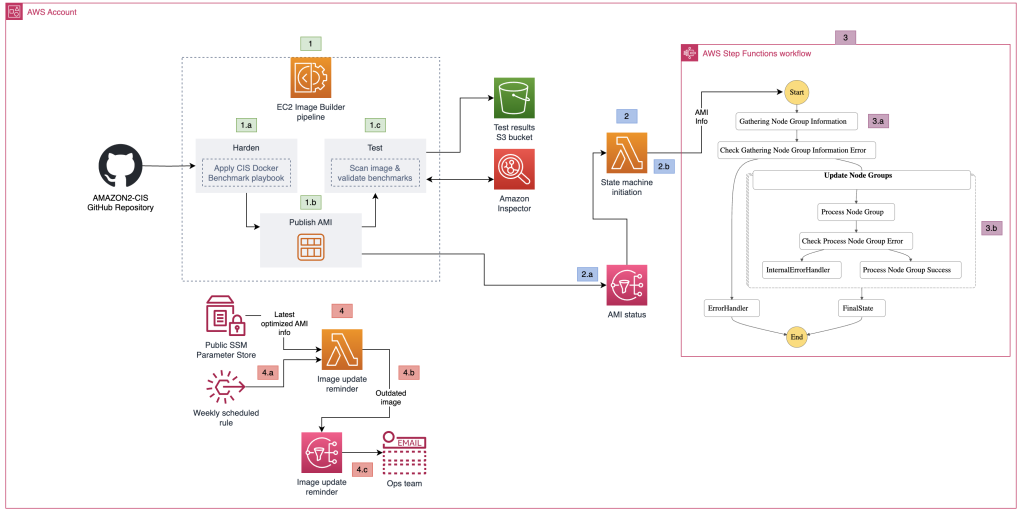
How to create a pipeline for hardening Amazon EKS nodes and automate updates
July 16, 2024: We updated the code in this post and some of the CloudFormation parameters. Amazon Elastic Kubernetes Service (Amazon EKS) offers a powerful, Kubernetes-certified service to build, secure, operate, and maintain Kubernetes clusters on Amazon Web Services (AWS). It integrates seamlessly with key AWS services such as Amazon CloudWatch, Amazon EC2 Auto Scaling, […]
Implementing a compliance and reporting strategy for NIST SP 800-53 Rev. 5
Amazon Web Services (AWS) provides tools that simplify automation and monitoring for compliance with security standards, such as the NIST SP 800-53 Rev. 5 Operational Best Practices. Organizations can set preventative and proactive controls to help ensure that noncompliant resources aren’t deployed. Detective and responsive controls notify stakeholders of misconfigurations immediately and automate fixes, thus […]
How to implement single-user secret rotation using Amazon RDS admin credentials
You might have security or compliance standards that prevent a database user from changing their own credentials and from having multiple users with identical permissions. AWS Secrets Manager offers two rotation strategies for secrets that contain Amazon Relational Database Service (Amazon RDS) credentials: single-user and alternating-user. In the preceding scenario, neither single-user rotation nor alternating-user rotation would […]
Integrating AWS Verified Access with Jamf as a device trust provider
In this post, we discuss how to architect Zero Trust based remote connectivity to your applications hosted within Amazon Web Services (AWS). Specifically, we show you how to integrate AWS Verified Access with Jamf as a device trust provider. This post is an extension of our previous post explaining how to integrate AWS Verified Access […]
Investigating lateral movements with Amazon Detective investigation and Security Lake integration
According to the MITRE ATT&CK framework, lateral movement consists of techniques that threat actors use to enter and control remote systems on a network. In Amazon Web Services (AWS) environments, threat actors equipped with illegitimately obtained credentials could potentially use APIs to interact with infrastructures and services directly, and they might even be able to use […]
Authorize API Gateway APIs using Amazon Verified Permissions with Amazon Cognito or bring your own identity provider
August 9, 2024: This post has been updated to reflect a new feature in Amazon Verified Permissions that supports OpenID Connect (OIDC) compliant identity providers as identity source Externalizing authorization logic for application APIs can yield multiple benefits for Amazon Web Services (AWS) customers. These benefits can include freeing up development teams to focus on […]
TLS inspection configuration for encrypted egress traffic and AWS Network Firewall
In the evolving landscape of network security, safeguarding data as it exits your virtual environment is as crucial as protecting incoming traffic. In a previous post, we highlighted the significance of ingress TLS inspection in enhancing security within Amazon Web Services (AWS) environments. Building on that foundation, I focus on egress TLS inspection in this […]
How to generate security findings to help your security team with incident response simulations
April 8, 2024: We have updated the post to revise the CloudFormation launch stack link to provision the CloudFormation template. Continually reviewing your organization’s incident response capabilities can be challenging without a mechanism to create security findings with actual Amazon Web Services (AWS) resources within your AWS estate. As prescribed within the AWS Security Incident […]
Securing generative AI: data, compliance, and privacy considerations
Generative artificial intelligence (AI) has captured the imagination of organizations and individuals around the world, and many have already adopted it to help improve workforce productivity, transform customer experiences, and more. When you use a generative AI-based service, you should understand how the information that you enter into the application is stored, processed, shared, and […]